
Understanding the IT Equipment Refresh Cycle
In today’s fast-paced digital environment, staying technologically current isn’t optional — it’s essential. The IT equipment refresh cycle refers to the strategic process organizations use
West Coast: (800) 700-7683 — East Coast: (800) 821-1782 — Local: (909) 466-7680 — 9033 9th St. Rancho Cucamonga, CA 91730
Whether you’re a business looking to recover value from retired assets or an individual hunting for affordable tech, our guides and insights help you make smarter decisions in the IT resale market.

In today’s fast-paced digital environment, staying technologically current isn’t optional — it’s essential. The IT equipment refresh cycle refers to the strategic process organizations use

Why Data Security in ITAD Matters Every business that manages IT assets—servers, laptops, storage arrays, networking gear—ultimately faces one unavoidable challenge: how to securely dispose

Why ITAD Chain of Custody Isn’t Optional The modern enterprise stores its most sensitive information on IT equipment — from servers and laptops to storage

Understanding ITAD and Its Growing Importance Information Technology Asset Disposition (ITAD) refers to the policies, processes, and practices organizations use to securely and responsibly retire,

IT Asset Management is no longer just an internal IT process. It has become a business-critical strategy that impacts security, compliance, budgeting, and operational efficiency.
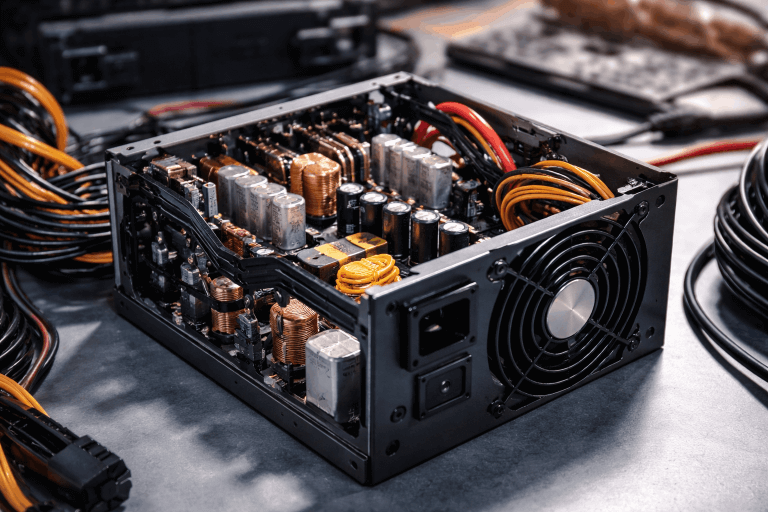
Why Understanding a PSU Matters In every computing system—from desktops to enterprise servers—the Power Supply Unit (PSU) plays a role as vital as the processor
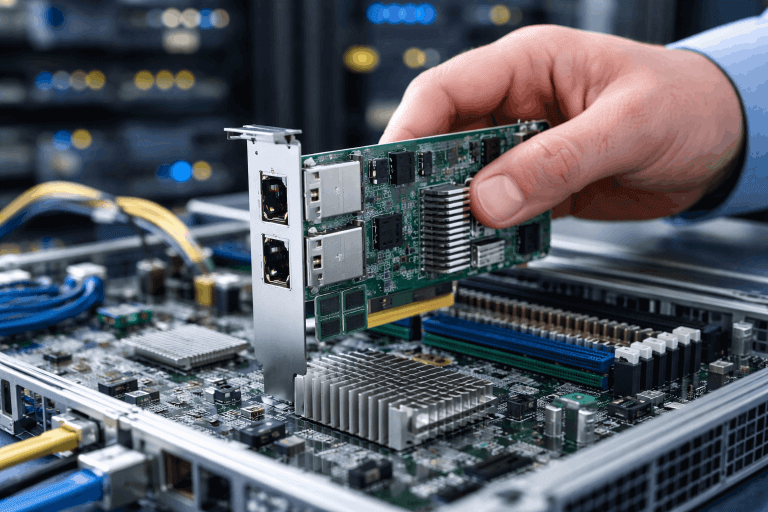
What Is a Network Interface Card? A Network Interface Card (NIC) is a foundational piece of hardware that enables computers, servers, and other devices to
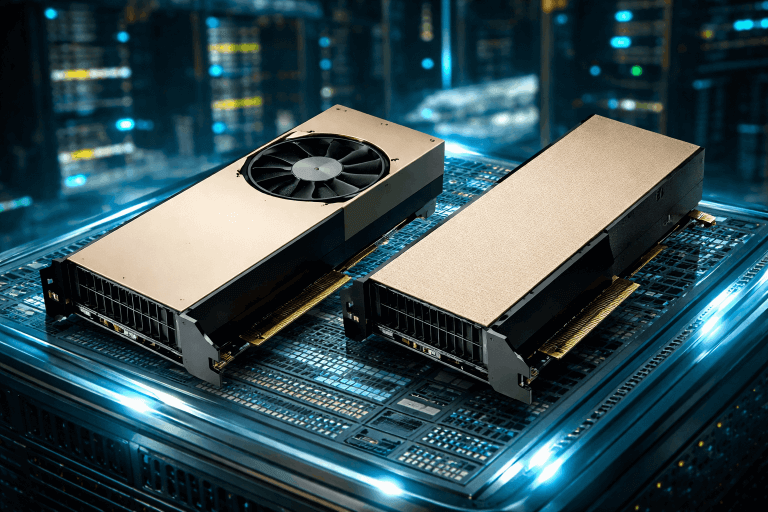
Today’s AI landscape relies heavily on powerful GPUs to train models, run inference, and support high-performance computing tasks across enterprises and research labs. Two of

Selling a used laptop in 2026 can be a smart way to put extra cash back in your pocket while extending the life of your
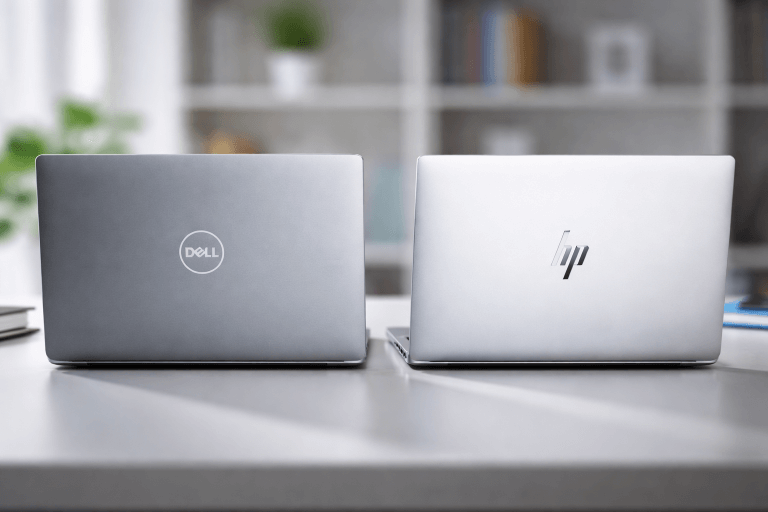
Why Dell vs HP Matters in 2026 Choosing between Dell and HP isn’t just about picking a laptop or server brand. For IT leaders, procurement

Key Takeaways: Turn Retired Servers into Strategic Value When it comes to retiring old IT assets in your organization, it’s not just about what to

Key Takeaways: Turn Retired IT Hardware into Cash Recycling electronics for cash isn’t just about disposing of obsolete devices for financial value—it’s also a strategic